Phone Verification Portal Check by Phone Number Exploring Safe Contact Signals
A discussion about phone verification portals examines safe contact signals without exposing sensitive data. The focus is on consistency, recency, and source credibility, evaluated through privacy-preserving checks. Validation covers format, carrier history, and risk indicators, guiding accept, escalate, or reject decisions. The approach remains auditable, resilient, and governed by risk thresholds. Anomalies trigger isolation and secondary verification, preserving data integrity while signaling what to scrutinize next. The topic invites further scrutiny of how signals influence trust and safeguards.
What Is a Safe Phone Verification Portal?
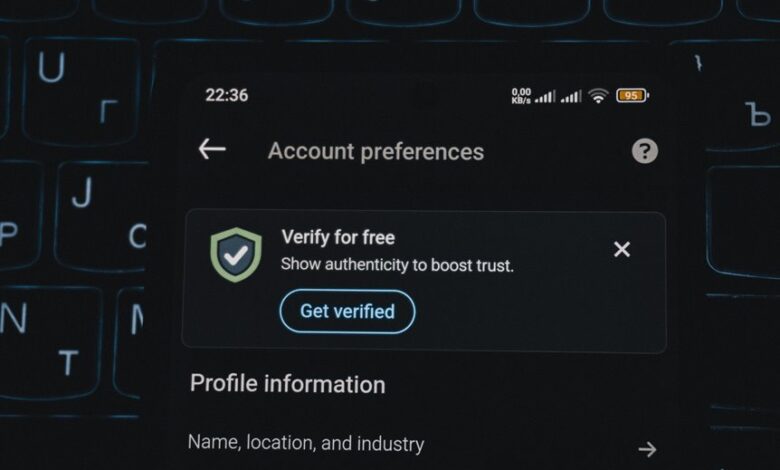
A safe phone verification portal is a trusted interface that confirms user identity through verified phone-based evidence, while enforcing strict security controls to protect data integrity and privacy.
The system emphasizes resilience, auditable processes, and minimal exposure. It enables safe contact and rapid risk assessment through precise verification signals, consolidating authentication layers without revealing sensitive content.
Clear governance supports freedom within protected boundaries.
How to Evaluate a Verification Signal by Phone Number
Evaluating a verification signal by phone number requires a disciplined, evidence-based approach that builds on the established safe verification framework. Verification signals are assessed through consistency, recency, and source credibility, emphasizing privacy-preserving checks.
Phone number validation focuses on format, carrier history, and risk indicators without exposing personal data. Conclusions guide secure acceptance, rejection, or escalation within a controlled verification workflow.
Common Red Flags in Verification Portals and How to Respond
Common red flags in verification portals include inconsistent or missing data fields, atypical request patterns, and suspicious success indicators that contradict prior validation steps. The analysis identifies fraud indicators and emphasizes safeguarding user privacy. Respondents should document anomalies, isolate suspicious sessions, and request secondary verification. A proactive stance preserves freedom, reduces risk, and strengthens trust without compromising essential data control.
Practical Steps to Verify Legitimacy Without Sharing Personal Data
To verify legitimacy without exposing personal data, practitioners should rely on objective signals that do not require sharing sensitive information. Structured review methods enable independent assessment, avoiding disclosure while maintaining accountability.
Durable verify signals include portal watermark integrity, transaction parity, timing consistency, and source authentication checks. Document findings, compare against baselines, and apply risk-based thresholds for safe, informed decisions.
Conclusion
A Secure Verification Portal stands as a locked vault, its hinges forged from privacy-first checks and auditable steps. Signals drift like quiet sentinels—consistency, recency, source credibility—each weighing risk without unveiling sensitive data. When anomalies appear, the system isolates them, reroutes through secondary verification, and logs every maneuver. The result is a precise, resilient workflow: gatekeepers who balance access with safeguards, guiding users through verification like a lighthouse steady against dark, unseen currents.




