Caller Trace Research Node Check This Number Exploring Verified Lookup Insights
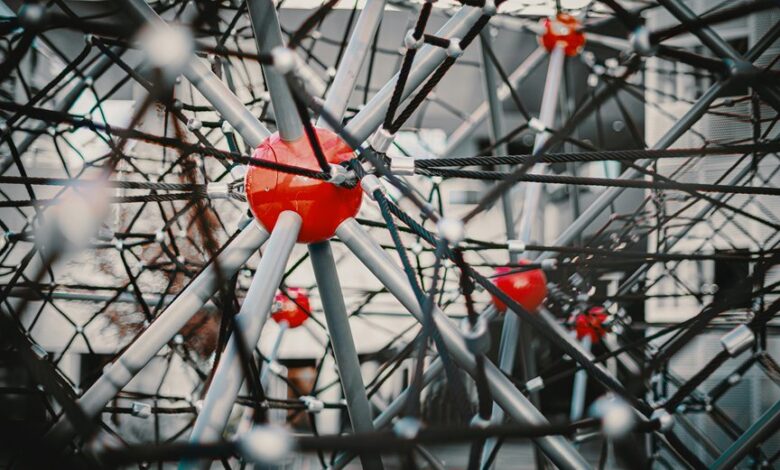
The Caller Trace Research Node Check This Number aggregates teleco registry signals, carrier metadata, and public reports to validate call origins and routes. It cross-checks timestamps, frequency patterns, and provenance fingerprints to generate deterministic risk scores while preserving privacy. The approach emphasizes governance, consent, and data minimization to support auditable, secure routing decisions. Yet questions remain about anomaly handling, scalability, and the implications for privacy-preserving traceability that warrant closer examination.
What Is Verified Lookup in Caller Tracing?
Verified lookup in caller tracing refers to a verified method for identifying the originating source and route of a phone call. The concept centers on attributing path data and source authentication to determine traceability. In practice, Verified lookup supports accountability, enabling consistent documentation. Analysts evaluate metadata integrity, routing logs, and carrier cooperation to ensure robust, auditable Caller tracing outcomes.
How the Check This Number Worker: Data Sources and Validation
How does the Check This Number worker source and validate data? The process aggregates signals from teleco registries, carrier metadata, and publicly reported numbers. Verification occurs through cross-referencing timestamps, frequency patterns, and anomaly scoring. Data sources feed a verification pipeline that flags discrepancies. The output supports verify lookup accuracy and facilitates caller tracing integrity without compromising privacy.
Getting Practical: Using Verified Lookup to Improve Trust and Routing
To operationalize verified lookup, practitioners integrate trust signals into routing decisions, aligning caller provenance with real-time risk assessments. The approach centers on quantified fingerprints, cross-validated data, and deterministic provenance scoring. Implementations emphasize interoperability, latency awareness, and scale. Verified lookup informs dynamic routing, reducing false positives. Caller tracing becomes a baseline capability enabling proactive damage control and auditable trust-anchors across networks.
Pitfalls, Privacy, and Ethics in Number Tracing
The shift from operationalized verified lookup to broader number tracing introduces meaningful concerns around privacy, data minimization, and user autonomy. In this context, privacy ethics guide governance models, ensuring transparent data flows and explicit consent. Data governance structures must address retention, access control, and auditability. Security concerns demand robust encryption, anomaly detection, and defined breach response to preserve trust and accountability.
Conclusion
In a landscape where numbers converge as data points, the coincidence of timestamps and carrier signals reveals a pattern: verified lookup, when disciplined by governance and consent, yields trustworthy provenance. The Check This Number worker cross-validates sources, aligning routes with anomaly scores to deter misdirection. Yet as the mesh tightens, privacy guards tighten in tandem. The surprising harmony between traceability and privacy emerges not as a compromise, but as a refined equilibrium guiding proactive, responsible routing decisions.




