Account Analysis Node c00hha0220120134 Exploring Digital Identity
The account analysis node c00hha0220120134 acts as a centralized evaluator of credential streams within the Identity Ecosystem. It traces data provenance, records timestamped transformations, and maps signals to verifiable outputs. The design emphasizes governance, risk management, and privacy-by-design principles. Its impact rests on auditable decision points and interoperable outcomes, but practical implementation reveals tradeoffs between transparency and performance. Stakeholders are left considering how governance controls scale under evolving data flows.
Account Analysis Node in the Identity Ecosystem
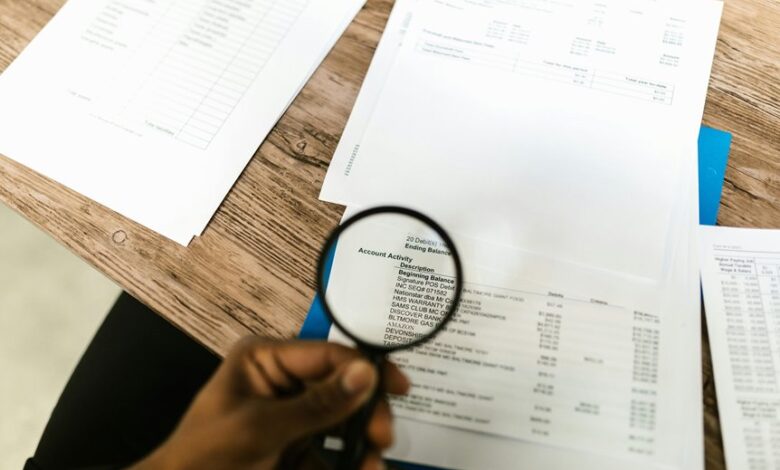
The Account Analysis Node functions as a central component within the Identity Ecosystem, methodically evaluating credential data streams to determine reliability and relevance. It supports identity verification through structured checks, tracks data provenance, and reinforces trust by auditing origin and integrity. The node emphasizes security and compliance in the node, ensuring governance, risk management, and auditable accountability across interactions.
Data Flow Through c00hha0220120134 in Practice
Data flows within c00hha0220120134 are mapped to a structured sequence of checks that translate credential streams into verifiable signals. In practice, data provenance is tracked, transformations are documented, and intermediate results are timestamped. The process aligns with privacy governance principles and data minimization, ensuring only necessary attributes are retained, enabling auditable verification while preserving user autonomy and analytical clarity.
Trust, Security, and Compliance in the Node
What assurances underlie the node’s operation, and how are trust, security, and compliance integrated into its governance? The analysis locates governance in formalized privacy governance structures, risk assessment protocols, and continuous monitoring. It emphasizes auditable decisions, access controls, and separation of duties. Compliance mapping aligns with applicable standards, while risk assessment informs remediation prioritization, emphasizing resilience, accountability, and freedom from unlawful intrusion.
Practical Deployment: Integration Patterns, Pitfalls, and Metrics
Practical deployment requires a disciplined evaluation of integration patterns, potential pitfalls, and measurable metrics to assess operational viability. The analysis separates architectural options from implementation risks, emphasizing interoperability, security seams, and governance controls. It notes privacy concerns as a design constraint, champions latency optimization, and prioritizes monitoring, incident response, and continuous improvement to sustain predictable performance in dynamic identity ecosystems.
Conclusion
The Account Analysis Node c00hha0220120134 provides a disciplined framework for evaluating credential data streams, tracing provenance, and recording auditable transformations with precise timestamps. It emphasizes privacy-by-design, governance, and continuous monitoring to sustain interoperable identity outcomes. Although critics may doubt the practicality of pervasive provenance, the system’s modular mappings to verifiable signals demonstrate measurable improvements in trust, security, and compliance. In practice, rigorous data flow governance yields resilient decision-making and auditable accountability at scale.




