Phone Verification Hub Check Spam Phone Number Revealing Trusted Data
A Phone Verification Hub evaluates numbers by triangulating auditable signals. It aims to reveal trusted data while guarding privacy, distinguishing legitimate contacts from red flags. The method relies on credible sources and cross-checks, yet remains skeptical of noisy signals. Speed must not outpace verification, and transparency should not expose sensitive details. The balance raises questions about provenance, scope, and accountability, leaving watchers with an unsettled sense of certainty and a need to scrutinize the processes more closely.
What a Phone Verification Hub Do for You
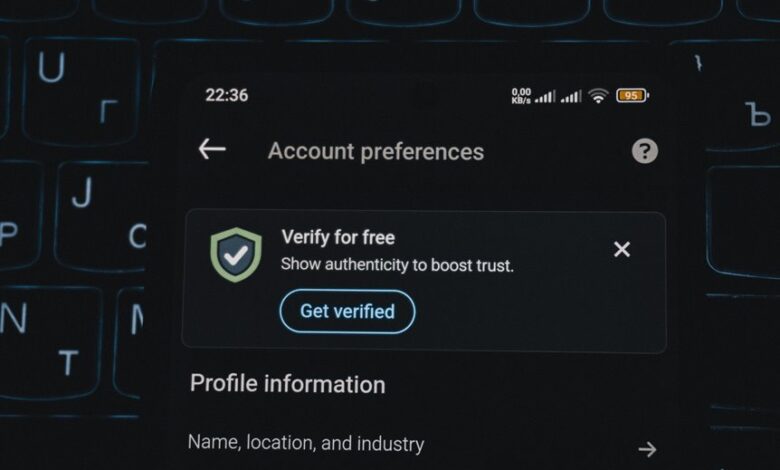
A phone verification hub serves as an intermediary that validates number authenticity and shields users from misdialed or fraudulent activity. It operates by cross-checking signals, confirming ownership, and preserving data integrity while remaining minimally invasive. The system enables access with auditable transparency, invites scrutiny, and promotes freedom through reliable pathways. Yet skepticism remains about privacy trade-offs and centralized control in verification processes.
Spotting Legitimate Numbers vs. Red Flags
Spotting legitimate numbers and red flags requires a methodical approach: what patterns reliably indicate trust, and which cues signal risk?
The assessment hinges on spot verification beyond appearance, noting privacy tradeoffs and the burden of data collection.
Cross checking data strengthens assessments, but source reliability remains heterogeneous; skepticism preserves freedom while avoiding overconfidence in surface signals or opaque origins.
Verifying Data: Trusted Sources and Cross-Checks
Verification hinges on triangulation: do multiple independent sources converge on the same data, and are those sources suitably credible? Verifiers examine glossary terms and data provenance to map chains of custody. Cross checks illuminate inconsistencies, while source validation excludes dubious origins. A disciplined approach prizes transparency, auditability, and coherent sourcing, yielding trusted conclusions and safeguarding freedom to rely on verified information.
Weighing Speed, Privacy, and Confidence in Results
Balancing speed, privacy, and confidence requires a careful assessment of trade-offs that emerge when verification processes run under time pressure while preserving user protections and evidentiary rigor.
The inquiry examines speed privacy implications without surrendering accountability, questioning whether rapid checks still yield reliable signals.
Skeptical analysis reveals how speed can undermine confidence results, urging transparent methodologies and robust privacy safeguards for freedom-minded users.
Conclusion
A Phone Verification Hub operates as a cautious referee, weighing signals from multiple sources before rendering judgment. It claims transparency and disciplined sourcing, yet remains vigilant for inconsistency and bias. The system promises speed without sacrificing privacy, but the reader should question where data provenance begins and ends. In a landscape of shifting trust, the hub’s method—triangulating auditable clues—reads like a skeptical compass, pointing toward truth while acknowledging blind spots and the limits of certainty.




